Satellite Communications Protection
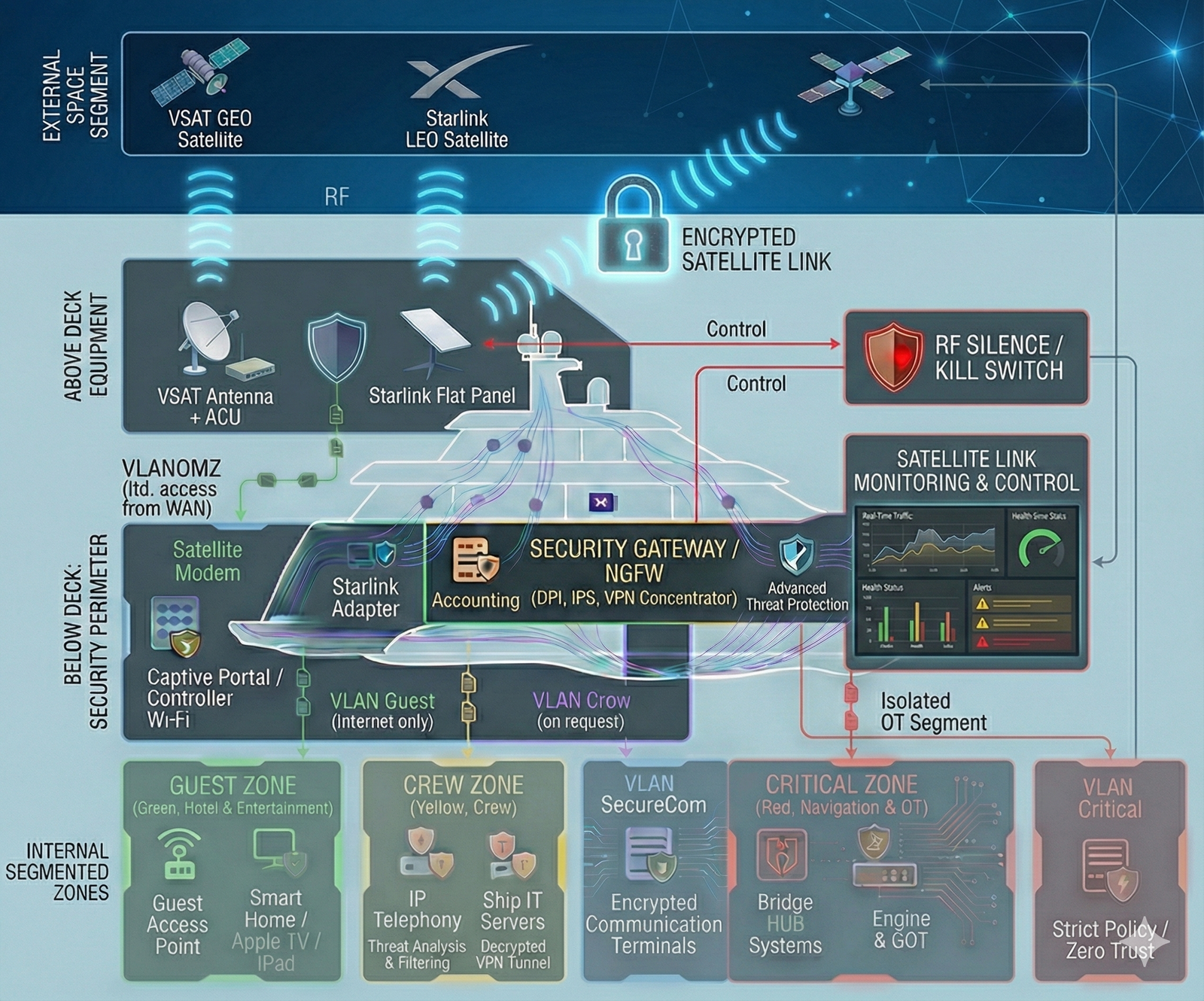
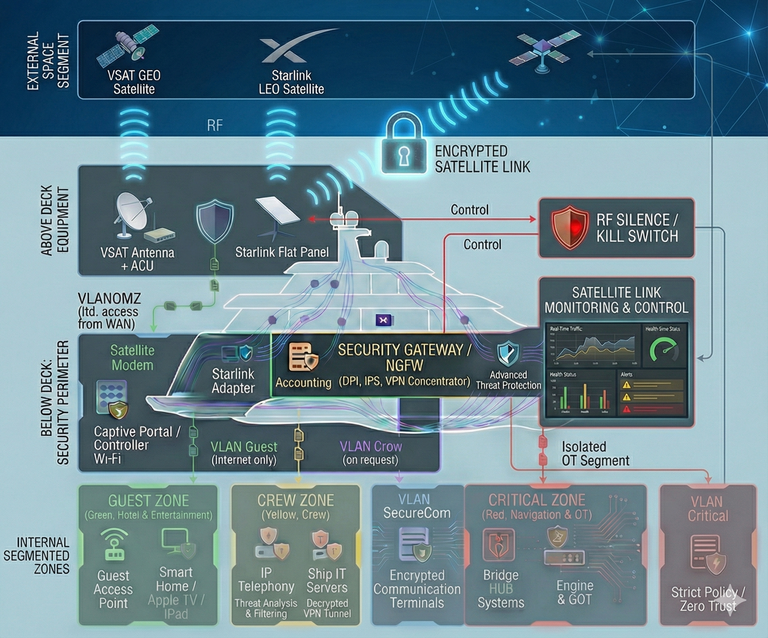
Solution Architecture: Layered Protection of Shipboard Satellite Communications
The solution architecture follows the principle of Defense-in-Depth, where the satellite link is treated as an Untrusted WAN. In modern maritime operations, satellite connectivity is critical for ship-to-shore communications, vessel management and operational continuity, while also representing a major cyber risk vector. Therefore, the security architecture is deployed inline between the vessel’s satellite equipment and the shipboard LAN.
Key architectural components
- Satellite Link Termination: Traffic from BDE (Below Deck Equipment — VSAT modems or Starlink/LEO terminals) is not delivered directly into the shipboard network. The first entry point is a dedicated Security Gateway / NGFW. It acts as a “digital bulkhead” separating external RF equipment from the vessel’s internal IT/OT environment.
- Cryptographic Gateway (VPN Concentrator): All operational and mission-critical traffic (shore office connectivity, telemetry, remote access for vendors/contractors and class) is encapsulated in secure VPN tunnels (IPsec/SSL) using modern cryptographic standards. VPN termination and decryption are performed exclusively on the controlled onboard gateway—not on end-user devices— reducing Man-in-the-Middle exposure over satellite and RF links.
- Segmented Routing: After inspection at the gateway, traffic is forwarded strictly into its designated isolated network segment (VLAN). “Open” Internet traffic (e.g., via LEO) is confined to passenger/guest zones only, while protected channels (e.g., VSAT with a corporate VPN) may access operational crew networks. Direct access from satellite links into critical zones (OT / Navigation / Vessel Control) is physically and logically blocked.
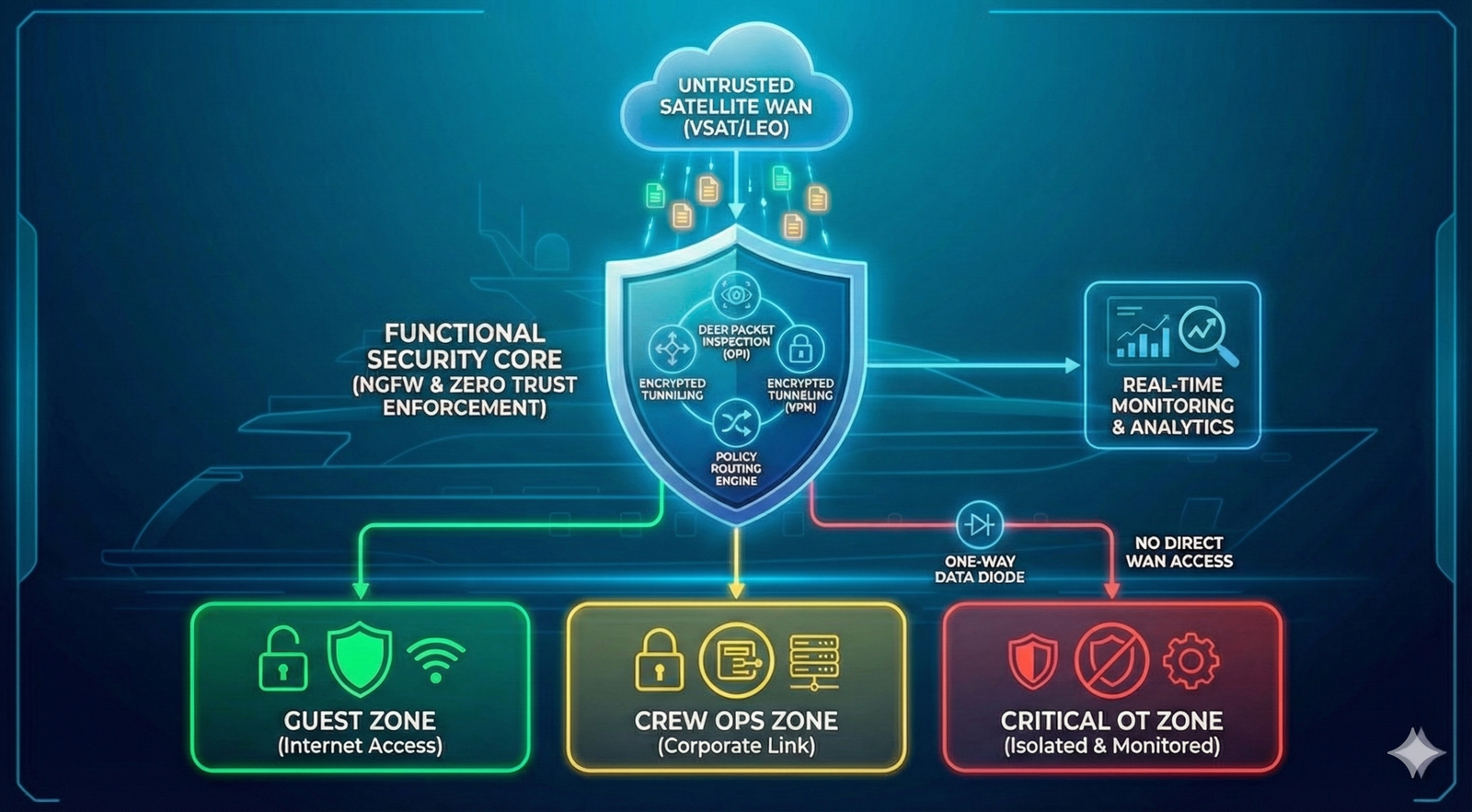
Functional Architecture: Secure Shipboard Satellite Gateway
The diagram describes the operating logic of the Secure Satellite Integration system. The solution securely aggregates satellite links (VSAT/LEO) and performs controlled “sanitisation” before traffic is allowed into the vessel’s internal network, enforcing a Zero Trust approach to external communications. In terms of navigational and operational safety, this means no external link is trusted by default and all data flows are verified and forcibly separated into zones.
1. External Segment & Emission Control (RF Layer)
At the physical layer, the system manages interaction with the space segment, treating the RF environment as potentially hostile, including interception, jamming and RF-based threat targeting considerations.
- Multi-orbit aggregation: Concurrent operation across GEO (VSAT GEO) and LEO (Starlink LEO) provides link redundancy, load balancing and resilient ship-to-shore connectivity.
- RF Silence / Kill Switch: A dedicated hardware module (RF Control Logic) allowing an operator to instantly de-energise antenna transmit paths. This reduces RF signature and prevents data transmission over RF links during critical situations (e.g., a security incident, suspected compromise, or procedural requirements).
2. Security Perimeter (Security Gateway Layer)
The central processing node (“Below Deck Security Perimeter”), where traffic is logically cleaned and security policies are enforced before data reaches the vessel’s IT/OT environment.
- Security Gateway (NGFW): A single ingress point for all satellite modems. Traffic is not routed directly; it is terminated at the gateway for inspection, filtering and session control.
- VPN Concentrator: VPN termination and decryption occur here. This enables inspection of encrypted payloads for malware and unauthorised activity before traffic reaches users or systems (visibility into threats inside encrypted traffic).
- DPI & IPS: Intrusion prevention analyses packet headers and content, blocking exploit attempts, C2/botnet activity and anomalous commands at an early stage.
3. Segmentation & Distribution (Internal Zones Layer)
After sanitisation, traffic is strictly distributed to isolated virtual networks (VLANs) based on security policies and operational roles. This prevents lateral movement and protects safety-critical ship functions.
- GUEST ZONE (Green Zone): Passenger/guest Internet and media access. Traffic is isolated from ship control and operational networks.
- CREW ZONE (Yellow Zone): Service network for crew operations and ship services. Access to corporate resources is provided via verified VPN tunnels and least-privilege policies.
- CRITICAL ZONE (Red Zone): Navigation and OT (Operational Technology) segment. Internet access is blocked or tightly constrained using whitelisting and one-way exchange mechanisms, reducing the risk of remote interference with safety-critical ship systems.